HomeOpen Privacy Suite
Open Privacy Suite
Open, vendor-lock-in-free privacy infrastructure for any EVM chain. Azure built in. Deploy on private or public networks, from Ethereum mainnet to custom rollups.
Control who sees what on your blockchain. ZK-proof authentication, hierarchical role-based access, selective disclosure, and compliance tooling. All running through a single JSON-RPC proxy.
Open Standard
No Vendor Lock-In
Standard JSON-RPC, no proprietary protocols
EVM Agnostic
Any EVM Stack
Geth, Erigon, Besu, Nethermind
Azure Built In
Microsoft Azure + Entra ID
Native SSO via Azure Entra ID
Any Chain
Private or Public
Permissioned networks to Ethereum mainnet
Privacy Proxy
Control Every RPC Interaction
A JSON-RPC proxy that sits between your applications and your EVM node. Every request is intercepted, filtered, and redacted based on the caller's role and organisation. Batch requests, multicall patterns, and transaction traces are all handled automatically.
Two modes of operation cover every deployment model: Private Chain mode for permissioned networks with direct RBAC enforcement, and Public Chain mode for Ethereum mainnet and public rollups using ZK proofs and bridging. Execution client agnostic: works with Geth, cdk-erigon, Besu, Nethermind, or any node exposing a standard JSON-RPC interface. Every request is intercepted, filtered, and redacted based on the caller's role and organisation. Batch requests, multicall patterns, and transaction traces are all handled automatically.
Authentication is handled via Microsoft Azure Entra ID SSO or Privado ID ZK proofs. The architecture is open and vendor-lock-in-free: standard JSON-RPC only, no proprietary protocols, no chain modifications. Redis-backed caching and session storage enable horizontal scaling. Response-level filtering ensures transaction lookups return no data for unauthorised users, event logs are scoped per caller, and error details are sanitised before reaching end users.
Two modes of operation cover every deployment model: Private Chain mode for permissioned networks with direct RBAC enforcement, and Public Chain mode for Ethereum mainnet and public rollups using ZK proofs and bridging. Execution client agnostic: works with Geth, cdk-erigon, Besu, Nethermind, or any node exposing a standard JSON-RPC interface. Every request is intercepted, filtered, and redacted based on the caller's role and organisation. Batch requests, multicall patterns, and transaction traces are all handled automatically.
Authentication is handled via Microsoft Azure Entra ID SSO or Privado ID ZK proofs. The architecture is open and vendor-lock-in-free: standard JSON-RPC only, no proprietary protocols, no chain modifications. Redis-backed caching and session storage enable horizontal scaling. Response-level filtering ensures transaction lookups return no data for unauthorised users, event logs are scoped per caller, and error details are sanitised before reaching end users.
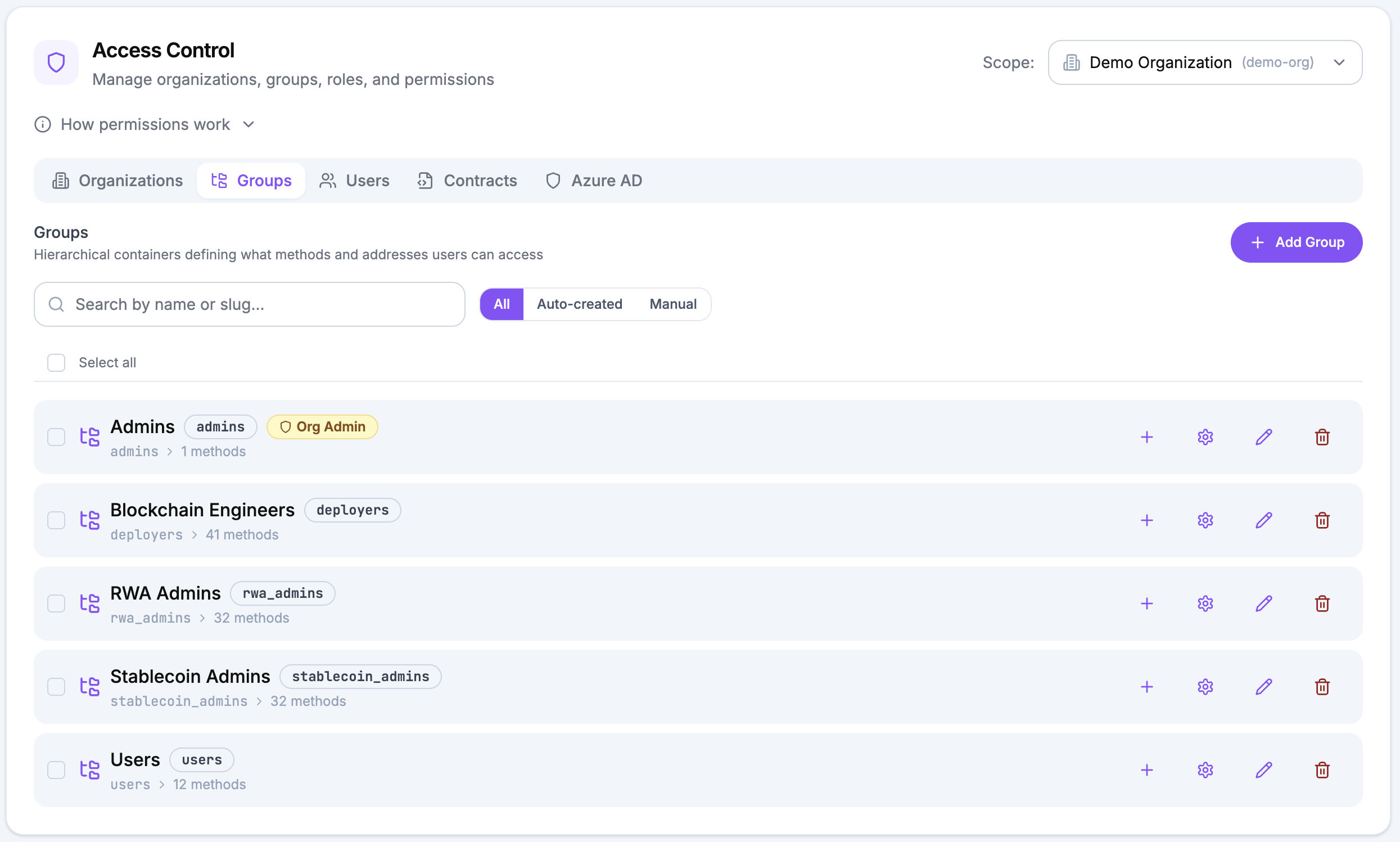
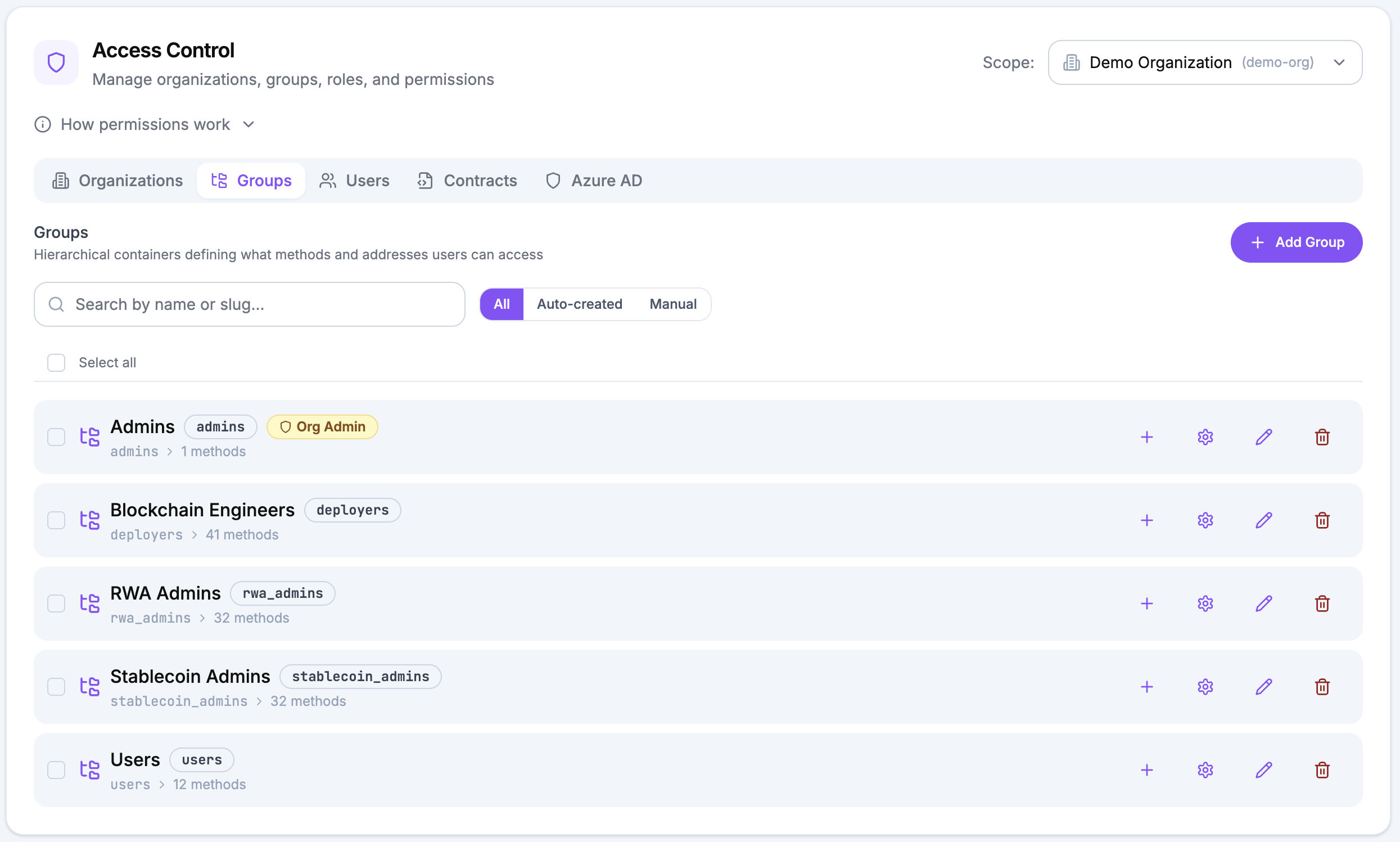
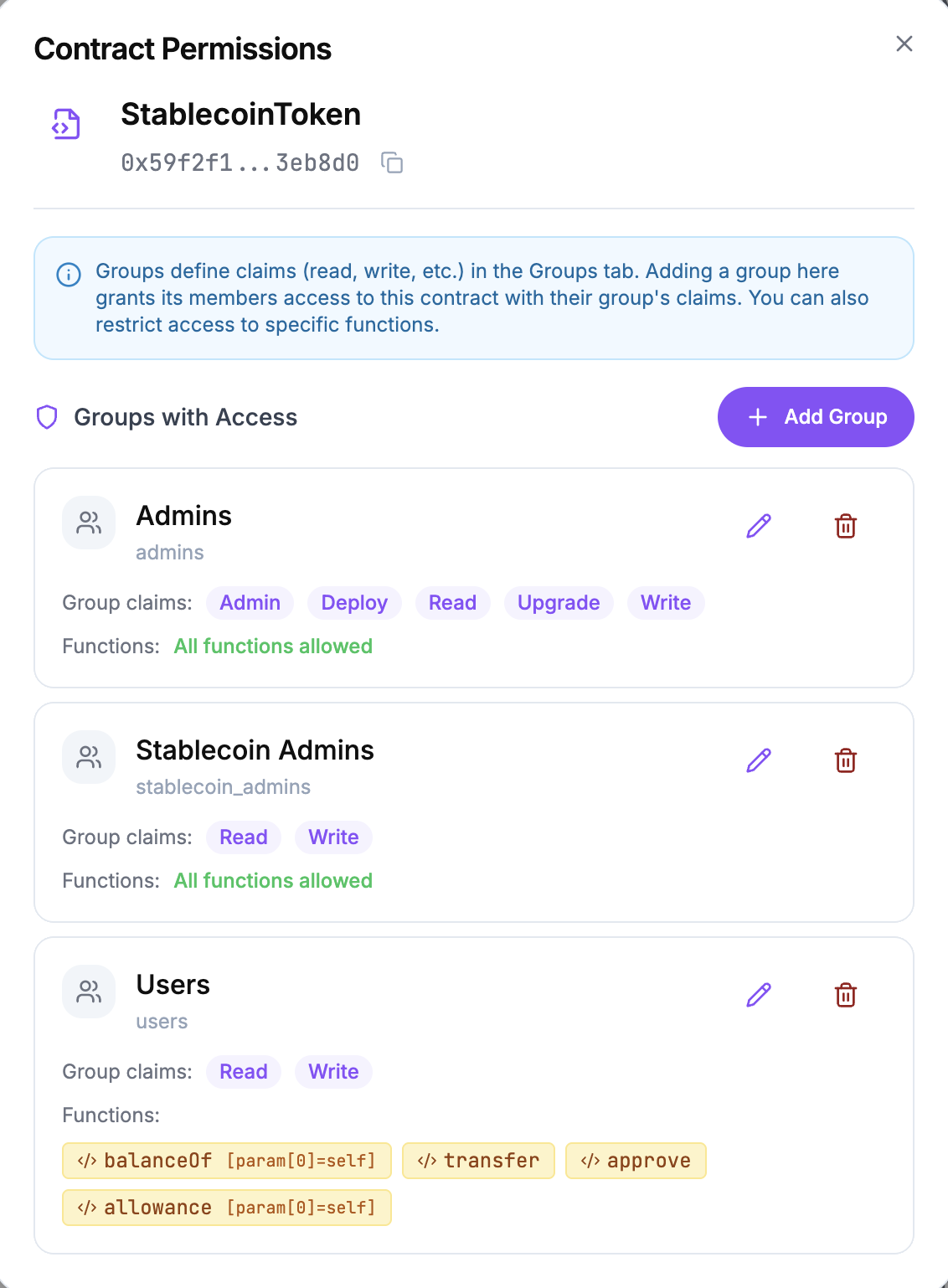
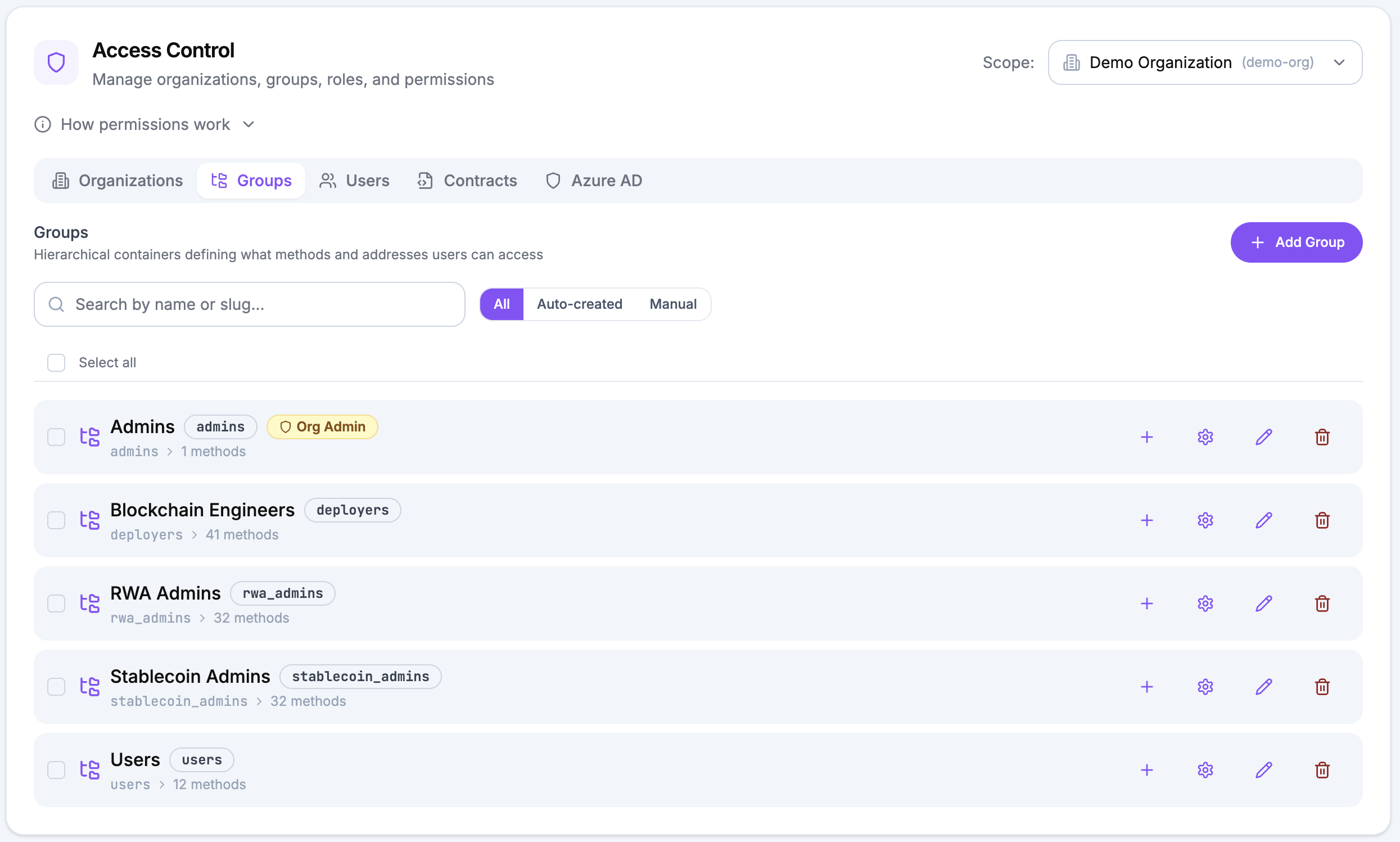
Role-Based Access Control
Hierarchical permissions from organisation down to individual function selectors. Admins grant themselves less, never more.
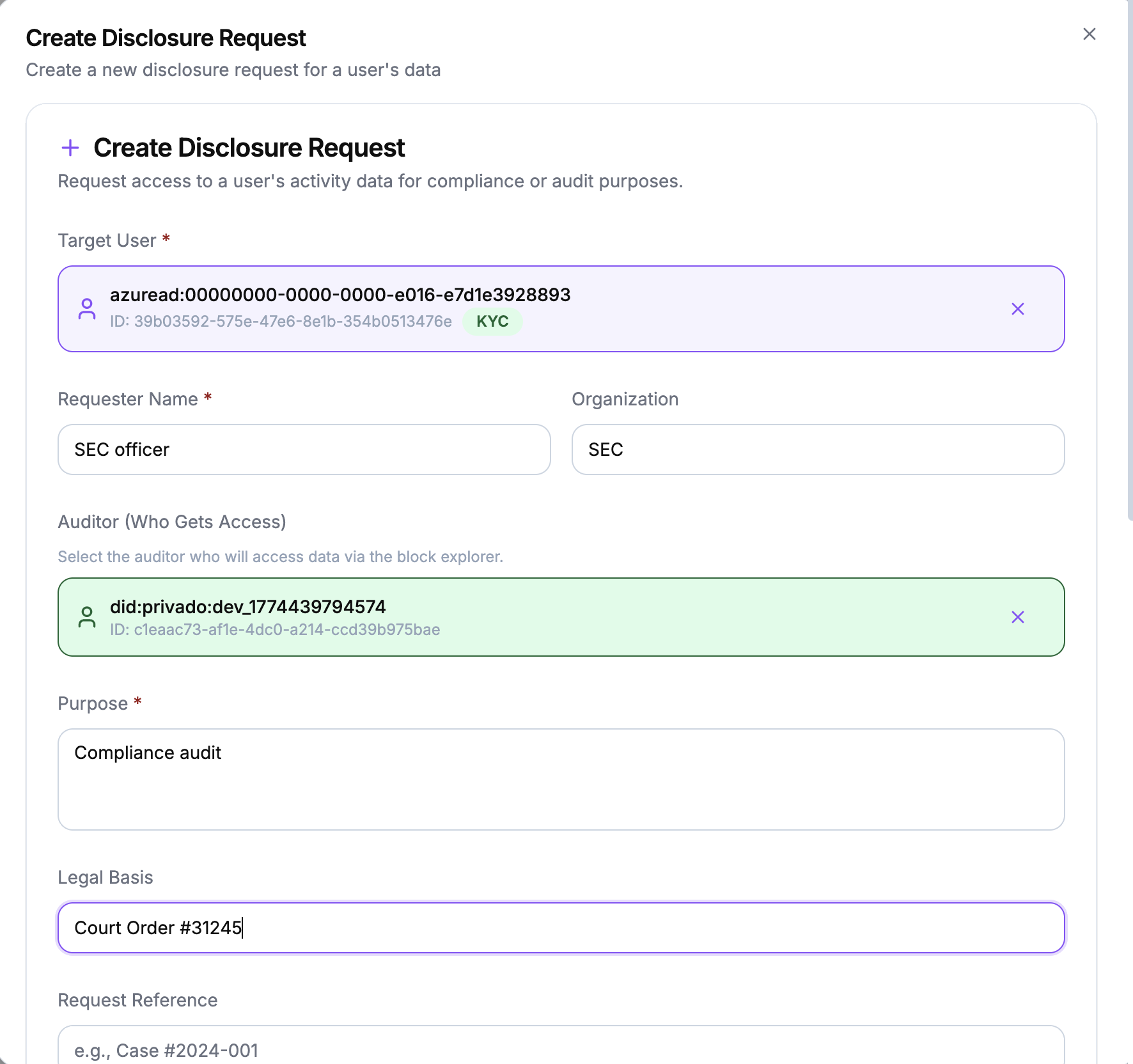
Selective Disclosure
Three disclosure levels per address: full visibility, consistent pseudonyms, or complete redaction. Time-limited grants with auto-expiry. Recipients approve or reject disclosure requests before visibility is granted.
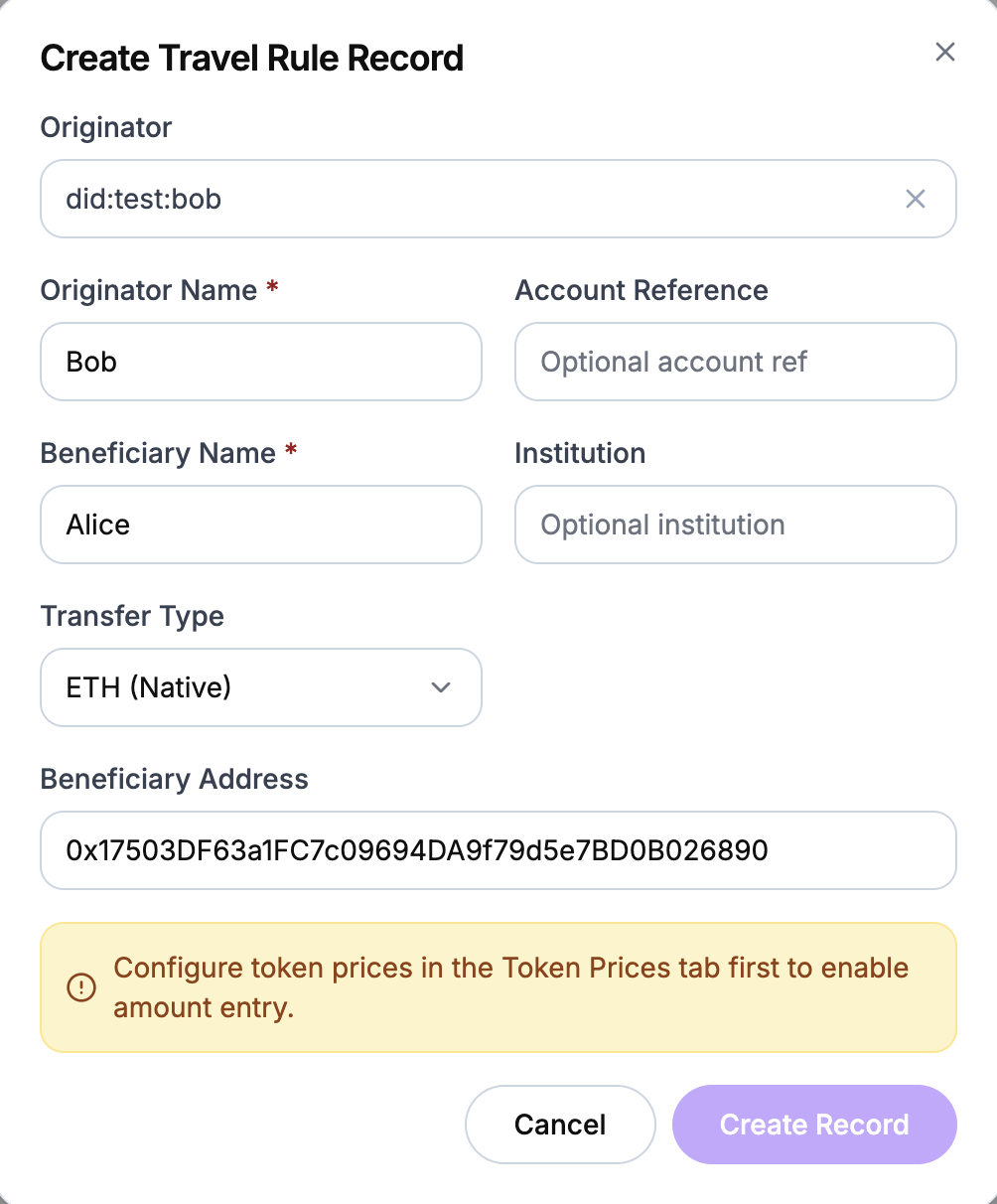
Compliance Built In
Travel rule enforcement, sanctions screening, and an immutable audit hashchain. Every decision is logged and forwarded to your SIEM.
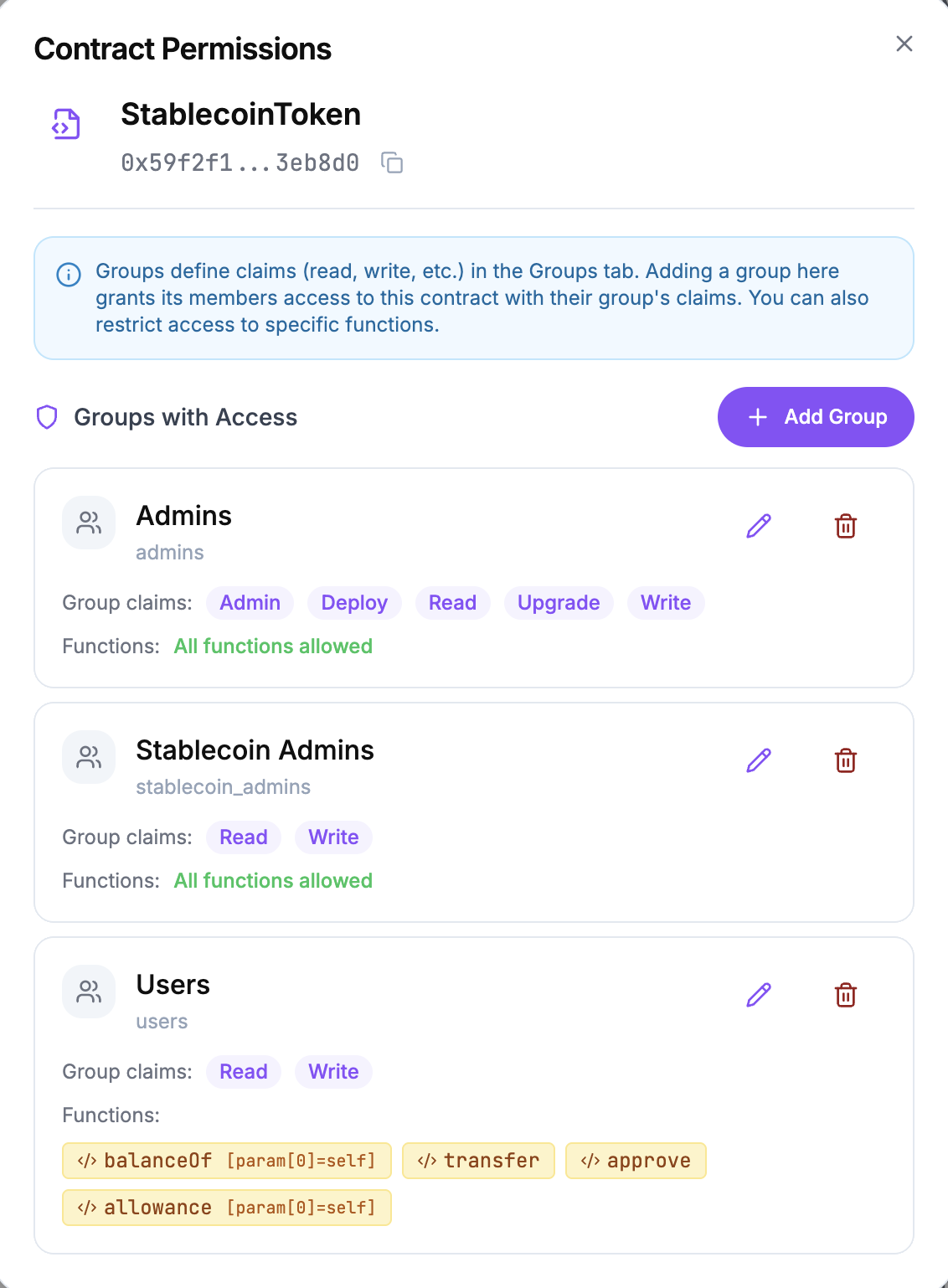
Hierarchical Access Control
Permissions cascade from organisation to group to user, with restrictive inheritance. Each level can only narrow the scope granted by its parent. Org admins retain full override capability.
- Contract-centric permissions: read, write, admin, upgrade, and deploy claims
- Function selector-level access control restricts by specific function signatures
- Parameter-level constraints on function arguments for granular enforcement
- Self-grant narrowing prevents privilege escalation
- Batch group management with granular method categories for efficient bulk operations
- Opaque denial responses return generic "not found" to prevent information leakage
Pluggable Authentication
Choose the authentication provider that fits your organisation. Both options work independently or together, and can be swapped without changing your access control configuration.
ZK-Proof Auth via Privado ID
QR code wallet flow with JWZ tokens. Users prove identity without revealing personal data. No centralised identity provider required.
Microsoft Azure Entra ID SSO
Enterprise SSO via Microsoft Azure Entra ID with per-organisation tenant allowlists. Connects directly to your existing Azure identity infrastructure. JWT access and refresh tokens with configurable TTLs.
Both providers support ETH address linking via EIP-191 signature challenge, with ENS resolution and caching for linked addresses.
Compliance and Audit Infrastructure
Every transaction and access decision is recorded, verified, and available for regulatory review. Travel rule records, sanctions checks, and disclosure requests are managed through an intuitive dashboard with full audit trail.
Smart Contract Deployment Controls
Prevent uncontrolled contract deployments on your network. CREATE2 and CREATE3 opcodes are detected in bytecode and blocked by default. Only approved factories on your whitelist can deploy.
Trusted Factory Whitelist
Only approved factories can use CREATE2/CREATE3. Bytecode is scanned and CBOR metadata stripped to prevent false-positive detection.
ABI and Proxy Pattern Support
Upload ABIs, map function selectors, and track proxy upgrades (transparent and UUPS patterns). Deterministic address pre-registration for CREATE2/CREATE3 deployments.
Cross-Organisation Isolation
Runtime transaction tracing detects dynamic CALL opcodes to contracts outside the caller's organisation. Enforces strict boundaries between participants.
Admin Dashboard
A comprehensive React admin interface for managing organisations, groups, users, and contracts. Full lifecycle management from onboarding through to audit review.
- RBAC hierarchy visualisation with interactive grant management
- Disclosure request and approval workflows with full audit trail
- Travel rule record submission and sanctioned address management
- Token price configuration with CoinGecko feeds and manual overrides
- User self-service disclosure inbox to approve, reject, or revoke grants
- Access log with live auto-refresh for real-time operational visibility
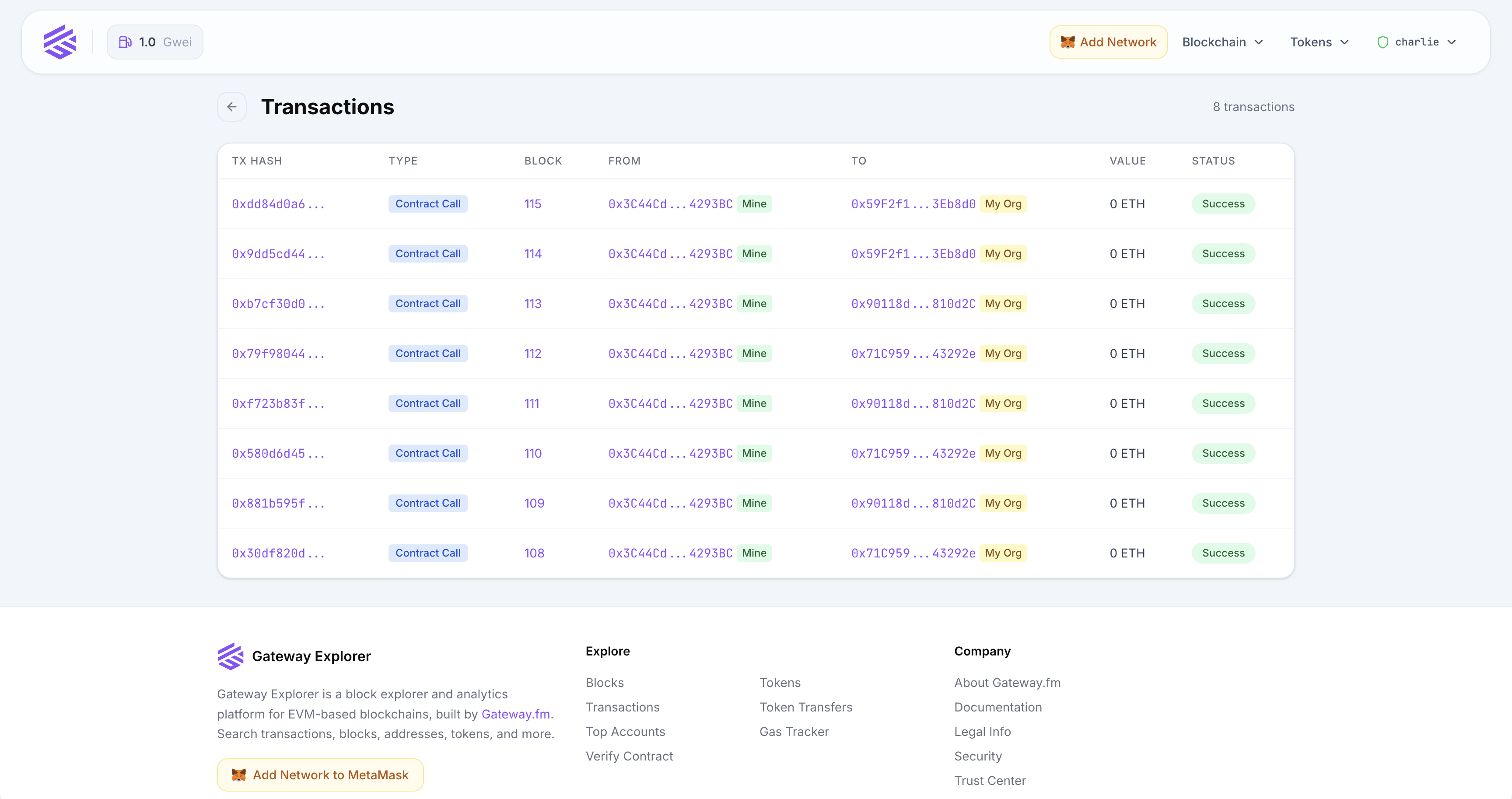
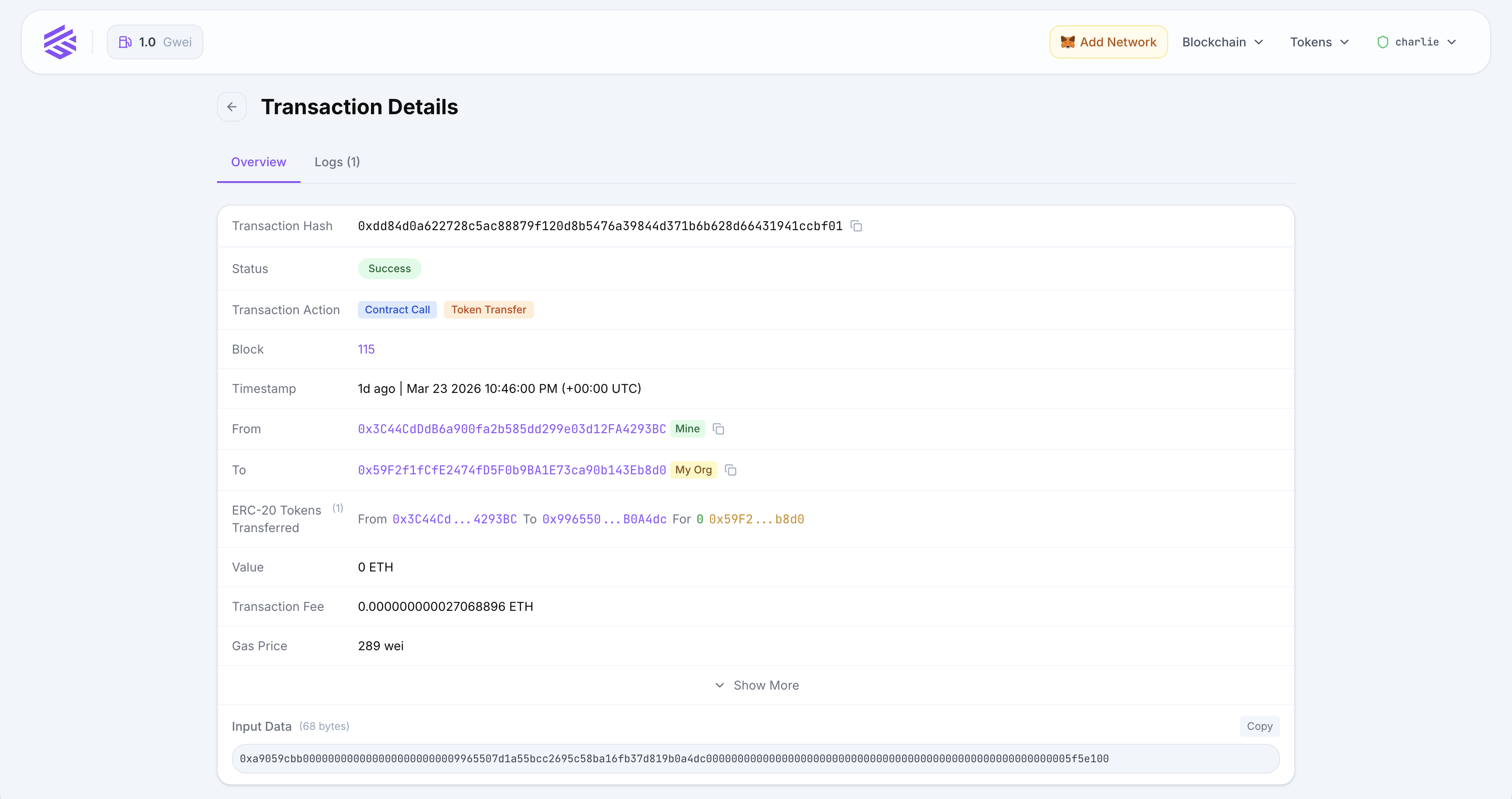
Privacy-Aware Block Explorer
A dedicated, private block explorer for any EVM-compatible chain, with built-in privacy controls. Point it at any RPC endpoint and it indexes blocks, transactions, logs, and internal calls in real time.
- Real-time indexing with parallel workers and configurable rate limits
- Historical backfill with gap detection and automatic requeue
- Local Solidity contract verification (v0.4 to v0.8) with Sourcify fallback
- Gas tracker with historical percentile calculations for accurate fee estimates
- Full-text search across blocks, addresses, and transactions with autocomplete
- L1 deposit fetching for OP Stack chains via Optimism Portal integration
- ERC-20 and ERC-721 token tracking with holder and transfer history
- Privacy dashboard: own, disclosed, and granted addresses with expiry tracking
API and Developer Experience
A comprehensive developer toolkit for building on top of the privacy layer, from REST endpoints to real-time streaming and CLI tooling.
A Unified Privacy Layer for Any EVM Chain
The Privacy Proxy and Block Explorer share authentication, disclosure grants, and access policies. Open and vendor-lock-in-free. Deploy on private or public chains with Microsoft Azure Entra ID or ZK-proof authentication built in.
Proxy to Explorer Privacy
Disclosure levels set in the Privacy Proxy are automatically enforced in the Block Explorer. A redacted address in your RPC responses is redacted in the explorer too.
Audit-Ready
Every RPC call and disclosure grant is logged to an immutable hashchain. One tamper-evident audit trail for your privacy infrastructure.
Enterprise-Integrated
SSO via Microsoft Azure Entra ID, ZK-proof authentication via Privado ID, and Prometheus metrics. Fits into your existing Azure identity and observability stack.
Built for Regulated Industries
Organisations running permissioned blockchains need privacy controls that satisfy regulators without sacrificing operational visibility.
See Open Privacy Suite in Action
Request a demoStart building today
Are you impressed? Let's talk!
Start small, prove the impact, and scale confidently as your project evolves.
Schedule a technical consultation
Provide us your technical requirements to get the best advice on architecture. Or simply clarify details.
Book a Call 24/7 Enterprise-Grade SLA Support
Uninterrupted operations around-the-clock
Deep Protocol Expertise
Precise customizations at a fundamental level
End-to-end vertically integrated stack
All layers. One provider
Modular. EVM-compatible
Plug-and-play components for any EVM chain

